文章目录
基于token的身份验证
JSON Web Token(JWT)是一个非常轻巧的规范。这个规范允许我们使用JWT在用户和服务器之间传递安全可靠的信息。
<!--JWT-->
<dependency>
<groupId>com.auth0</groupId>
<artifactId>java-jwt</artifactId>
<version>3.4.0</version>
</dependency>
个人理解
- 首先,登录的话,不能在通过shiro自己的方法去验证了,因为我们自定义的token需要存储用户使用的token,所以登录的密码验证就不能通过shiro进行验证,而需要我们自己去验证密码的准确性,在登录方法里面可以,在realm认证方法里面也可以.
- 然后,基于token进行权限验证的话,我们请求所有需要认证的接口时候请求头里必须携带token,然后后端进行token认证,判断token是否合法是否过期等等…
- token的刷新,可以自定义返回code,返回新的token,来进行token刷新工作.
- token缓存在redis中,可以实现集群token的共享.可以使token的过期删除交给redis
- 我为了简单实现,刷新token和缓存redis就不实现了,只跟shiro整合部分写上去.
jwt工具类
部分信息:
标准中注册的声明(建议但不强制使用)
iss: jwt签发者
sub: jwt所面向的用户 //这个以后就是放我们登录的用户名
aud: 接收jwt的一方
exp: jwt的过期时间,这个过期时间必须要大于签发时间 //过期时间也可以放
nbf: 定义在什么时间之前,该jwt都是不可用的.
iat: jwt的签发时间
jti: jwt的唯一身份标识,主要用来作为一次性token,从而回避重放攻击
import com.auth0.jwt.JWT;
import com.auth0.jwt.JWTVerifier;
import com.auth0.jwt.algorithms.Algorithm;
import com.auth0.jwt.exceptions.JWTDecodeException;
import com.auth0.jwt.interfaces.DecodedJWT;
import java.util.Date;
import java.util.UUID;
public class JwtUtil {
private static final long EXPIRE_TIME = 60 * 60 * 1000;
/**
* 校验token是否正确
*
* @param token 密钥
* @param secret 用户的密码
* @return 是否正确
*/
public static boolean verify(String token, String username, String secret) {
try {
//根据密码生成JWT效验器
Algorithm algorithm = Algorithm.HMAC256(secret);
JWTVerifier verifier = JWT.require(algorithm)
.withClaim("username", username)
.build();
//效验TOKEN
DecodedJWT jwt = verifier.verify(token);
return true;
} catch (Exception exception) {
return false;
}
}
/**
* 获得token中的信息无需secret解密也能获得
*
* @return token中包含的用户名
*/
public static String getUsername(String token) {
try {
DecodedJWT jwt = JWT.decode(token);
return jwt.getClaim("username").asString();
} catch (JWTDecodeException e) {
return null;
}
}
/**
* 获得token中的信息无需secret解密也能获得
*
* @return token中包含的用户名
*/
public static Integer getUserId(String token) {
try {
DecodedJWT jwt = JWT.decode(token);
return jwt.getClaim("userId").asInt();
} catch (JWTDecodeException e) {
return null;
}
}
/**
* 获得tokenId
*
* @return uuid
*/
public static String getTokenId(String token) {
try {
DecodedJWT jwt = JWT.decode(token);
return jwt.getId();
} catch (JWTDecodeException e) {
return null;
}
}
/**
* 获取token过期时间
*
* @return 过期时间
*/
public static Date getExpiresAt(String token) {
try {
DecodedJWT jwt = JWT.decode(token);
return jwt.getExpiresAt();
} catch (JWTDecodeException e) {
return null;
}
}
/**
* 获取token签发时间
*
* @return 签发时间
*/
public static Date getIssuedAt(String token) {
try {
DecodedJWT jwt = JWT.decode(token);
return jwt.getIssuedAt();
} catch (JWTDecodeException e) {
return null;
}
}
/**
* 生成签名
*
* @param username 用户名
* @param secret 用户的密码
* @return 加密的token
*/
public static String sign(String username, String secret) {
Date date = new Date(System.currentTimeMillis() + EXPIRE_TIME);
Algorithm algorithm = Algorithm.HMAC256(secret);
String jwtId = UUID.randomUUID().toString();
// 附带username信息
return JWT.create()
.withJWTId(jwtId)
.withClaim("username", username)
.withExpiresAt(date)
.withIssuedAt(new Date())
.sign(algorithm);
}
public static void main(String[] args) {
String token = sign("aaa", "123456");
System.out.println("token" + token);
System.out.println(getTokenId(token));
System.out.println(getUserId(token));
System.out.println(getUsername(token));
System.out.println(getIssuedAt(token));
System.out.println(getExpiresAt(token));
System.out.println(verify(token, "aaa", "123456"));
}
}
自定义shiro的token:
import org.apache.shiro.authc.AuthenticationToken;
public class JwtToken implements AuthenticationToken {
private String token;
public JwtToken(String token) {
this.token = token;
}
@Override
public Object getPrincipal() {
return token;
}
@Override
public Object getCredentials() {
return token;
}
}
shiro部分修改
登录的修改:

realm的修改:

重写supports方法,token必须是JwtToken,源码:
import com.txn.dto.User;
import com.txn.util.JwtToken;
import com.txn.util.JwtUtil;
import lombok.extern.slf4j.Slf4j;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
@Slf4j
public class JwtShiroRealm extends AuthorizingRealm {
@Override
public boolean supports(AuthenticationToken token) {
return token instanceof JwtToken;
}
/**
* 认证
*/
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
log.info("-doGetAuthenticationInfo登录认证-");
String tokenStr = (String) token.getCredentials();
// 解密获得username,用于和数据库进行对比
String username = JwtUtil.getUsername(tokenStr);
log.info("登录的用户:" + username);
if ("admin".equals(username)) {
//数据库查出来的用户
User user = new User();
user.setId(1);
user.setUserName("admin");
user.setPassword("admin");
// ByteSource bytes = ByteSource.Util.bytes("1");
//验证密码是否正确
if (JwtUtil.verify(tokenStr, username, user.getPassword())) {
log.info("登录成功");
} else {
throw new UnknownAccountException("用户名密码错误");
}
SimpleAuthenticationInfo simpleAuthenticationInfo = new SimpleAuthenticationInfo(token.getCredentials(), token.getCredentials(), this.getName());
return simpleAuthenticationInfo;
}
return null;
}
/**
* 授权
*/
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
log.info("执行doGetAuthorizationInfo方法进行授权");
String username = JwtUtil.getUsername(principalCollection.toString());
log.info("登录的用户:" + username);
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
info.addRole("role_admin");
info.addStringPermission("user:add");
info.addStringPermission("user:list");
return info;
}
}
这时候登录的时候返回token部分修改完成了,现在还需要自定义filter,部分需要校验的方法都需要走自定义filter,filter的作用就是将前端请求头里的token取出进行登录,登录成功将token缓存到redis里面,然后进行认证的时候直接通过redis进行认证即可.可以将username作为key,token作为value,当然key必须是唯一的.
自定义filter:
import com.txn.exception.MyprojectException;
import com.txn.util.JwtToken;
import org.apache.shiro.web.filter.authc.BasicHttpAuthenticationFilter;
import org.springframework.http.HttpStatus;
import org.springframework.util.StringUtils;
import org.springframework.web.bind.annotation.RequestMethod;
import javax.servlet.ServletRequest;
import javax.servlet.ServletResponse;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
public class JwtFilter extends BasicHttpAuthenticationFilter {
/**
* 执行登录认证
*
* @param request
* @param response
* @param mappedValue
* @return
*/
@Override
protected boolean isAccessAllowed(ServletRequest request, ServletResponse response, Object mappedValue) {
String token = ((HttpServletRequest) request).getHeader("Authorization");
if (StringUtils.isEmpty(token)) {
throw new MyprojectException("token不能为空");
}
// executeLogin(request, response);
return true;
}
/**
*
*/
@Override
protected boolean executeLogin(ServletRequest request, ServletResponse response) throws Exception {
HttpServletRequest httpServletRequest = (HttpServletRequest) request;
String token = httpServletRequest.getHeader("Authorization");
if (StringUtils.isEmpty(token)) {
throw new MyprojectException("token不能为空");
}
JwtToken jwtToken = new JwtToken(token);
// 提交给realm进行登入,如果错误他会抛出异常并被捕获
getSubject(request, response).login(jwtToken);
// 如果没有抛出异常则代表登入成功,返回true
return true;
}
@Override
protected boolean onAccessDenied(ServletRequest request, ServletResponse response) throws Exception {
System.out.println("登录失败");
return super.onAccessDenied(request, response);
}
/**
* 对跨域提供支持
*/
@Override
protected boolean preHandle(ServletRequest request, ServletResponse response) throws Exception {
HttpServletRequest httpServletRequest = (HttpServletRequest) request;
HttpServletResponse httpServletResponse = (HttpServletResponse) response;
httpServletResponse.setHeader("Access-control-Allow-Origin", httpServletRequest.getHeader("Origin"));
httpServletResponse.setHeader("Access-Control-Allow-Methods", "GET,POST,OPTIONS,PUT,DELETE");
httpServletResponse.setHeader("Access-Control-Allow-Headers", httpServletRequest.getHeader("Access-Control-Request-Headers"));
// 跨域时会首先发送一个option请求,这里我们给option请求直接返回正常状态
if (httpServletRequest.getMethod().equals(RequestMethod.OPTIONS.name())) {
httpServletResponse.setStatus(HttpStatus.OK.value());
return false;
}
return super.preHandle(request, response);
}
}
配置:

源码:
package com.txn.config.jwt;
import com.txn.config.ShiroRealm;
import com.txn.config.ShiroSessionListener;
import net.sf.ehcache.CacheManager;
import org.apache.shiro.authc.credential.HashedCredentialsMatcher;
import org.apache.shiro.cache.MemoryConstrainedCacheManager;
import org.apache.shiro.mgt.DefaultSessionStorageEvaluator;
import org.apache.shiro.mgt.DefaultSubjectDAO;
import org.apache.shiro.realm.Realm;
import org.apache.shiro.session.SessionListener;
import org.apache.shiro.session.mgt.SessionManager;
import org.apache.shiro.session.mgt.eis.SessionDAO;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.apache.shiro.web.servlet.SimpleCookie;
import org.apache.shiro.web.session.mgt.DefaultWebSessionManager;
import org.crazycake.shiro.RedisCacheManager;
import org.crazycake.shiro.RedisManager;
import org.crazycake.shiro.RedisSessionDAO;
import org.springframework.cache.ehcache.EhCacheManagerFactoryBean;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import org.springframework.core.io.ClassPathResource;
import javax.servlet.Filter;
import java.util.ArrayList;
import java.util.Collection;
import java.util.HashMap;
/**
* @author <a href="mailto:15268179013@139.com">yida</a>
* @Version 2020-01-01 15:05
* @Version 1.0
* @Description ShiroConfig
*/
@Configuration
public class JwtShiroConfig {
@Bean
public DefaultWebSecurityManager securityManager() {
DefaultWebSecurityManager webSecurityManager = new DefaultWebSecurityManager();
//session管理
// webSecurityManager.setSessionManager(sessionManager());
//realm管理
webSecurityManager.setRealm(realm());
//缓存管理
webSecurityManager.setCacheManager(new MemoryConstrainedCacheManager());
//使用ehcache
// EhCacheManager ehCacheManager = new EhCacheManager();
// ehCacheManager.setCacheManager(getEhCacheManager());
// webSecurityManager.setCacheManager(ehCacheManager);
//redis实现
// webSecurityManager.setCacheManager(redisCacheManager());
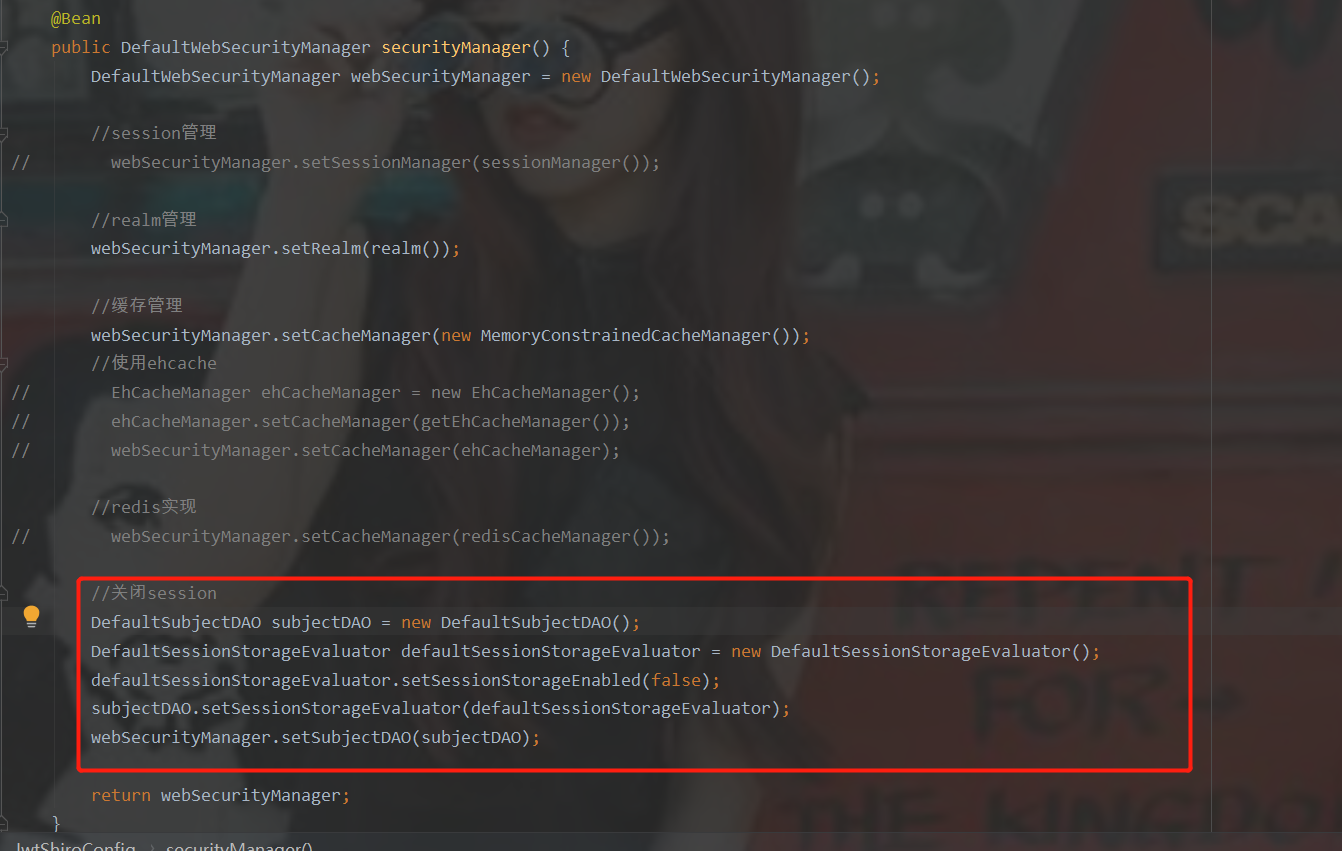
//关闭session
DefaultSubjectDAO subjectDAO = new DefaultSubjectDAO();
DefaultSessionStorageEvaluator defaultSessionStorageEvaluator = new DefaultSessionStorageEvaluator();
defaultSessionStorageEvaluator.setSessionStorageEnabled(false);
subjectDAO.setSessionStorageEvaluator(defaultSessionStorageEvaluator);
webSecurityManager.setSubjectDAO(subjectDAO);
return webSecurityManager;
}
@Bean
public RedisCacheManager redisCacheManager() {
RedisManager redisManager = new RedisManager();
redisManager.setHost("localhost:6379");
redisManager.setDatabase(1);
redisManager.setTimeout(5000);
// redisManager.setPassword();
RedisCacheManager redisCacheManager = new RedisCacheManager();
redisCacheManager.setRedisManager(redisManager);
return redisCacheManager;
}
@Bean
public CacheManager getEhCacheManager() {
EhCacheManagerFactoryBean ehCacheManagerFactoryBean = new EhCacheManagerFactoryBean();
ehCacheManagerFactoryBean.setConfigLocation(new ClassPathResource("classpath:org/apache/shiro/cache/ehcache/ehcache.xml"));
return ehCacheManagerFactoryBean.getObject();
}
@Bean
public Realm realm() {
JwtShiroRealm shiroRealm = new JwtShiroRealm();
return shiroRealm;
}
@Bean
public ShiroFilterFactoryBean shiroFilter() {
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
shiroFilterFactoryBean.setSecurityManager(securityManager());
shiroFilterFactoryBean.setLoginUrl("/login");
shiroFilterFactoryBean.setSuccessUrl("/index");
shiroFilterFactoryBean.setFilterChainDefinitions(
"/login = anon
" +
"/logout = logout
" +
"/user = jwt,authc,perms[user:list]
" +
"/** = jwt
" +
"");
HashMap<String, Filter> myFIleter = new HashMap<>();
myFIleter.put("jwt", new JwtFilter());
shiroFilterFactoryBean.setFilters(myFIleter);
return shiroFilterFactoryBean;
}
}
测试
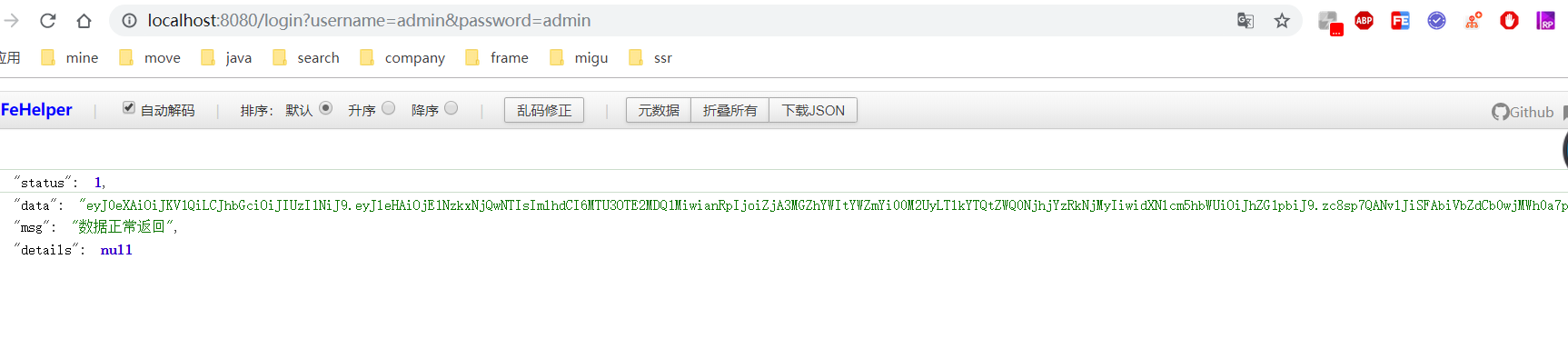
登录成功,返回token:
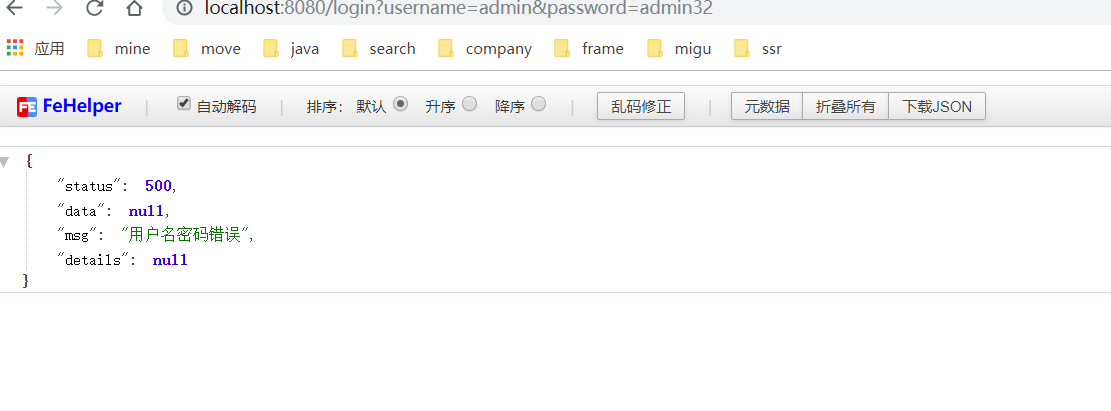
登录失败:
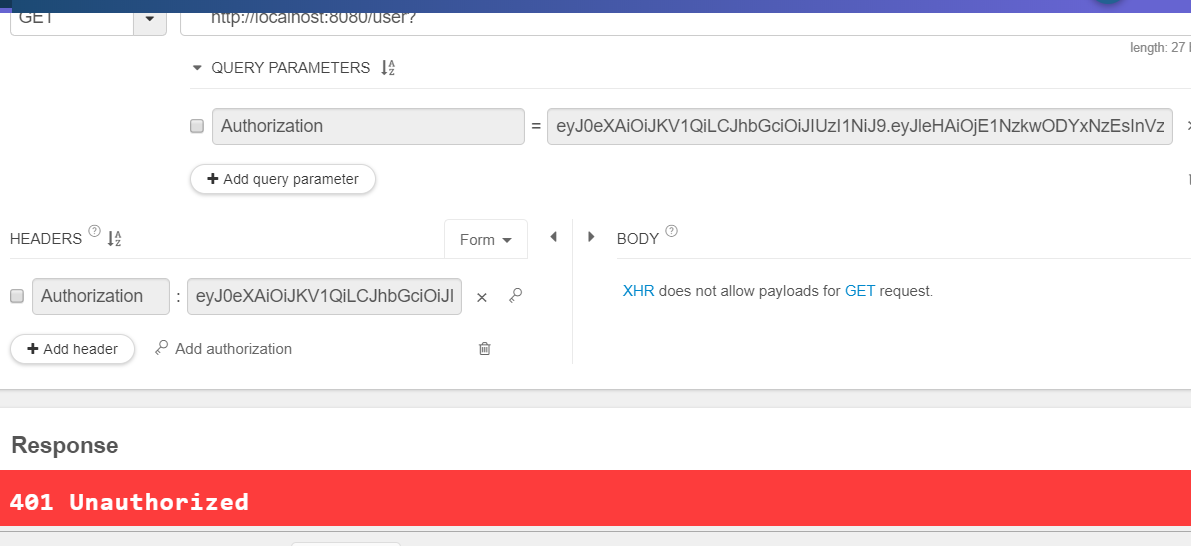
请求user:
携带token:

不携带返回401:
总结
简单的使用,具体项目中需要具体设计.我这里只是简单的使用,整合.
redis缓存的设计,token的刷新,等等,还需要根据项目进行设计,不过大体就是这样使用.










